Concerto CRT-D and Virtuoso ICD implantable cardiac devices are among several Medtronic electrophysiology devices included in a safety alert because of their lack of cybersecurity measures to avoid hacking, according to the FDA.
March 22, 2019 — The U.S. Food and Drug Administration (FDA) issued a safety communication to alert healthcare providers and patients about the cybersecurity vulnerabilities identified in a wireless telemetry technology used for communication between Medtronic’s implantable electrophysiology (EP) cardiac devices, clinic programmers and home monitors.
The FDA said a wireless telemetry protocol used for communication between the devices and their programming and monitoring systems has cybersecurity vulnerabilities because it does not use encryption, authentication or authorization. The FDA said this makes these system easy to hack into.
The FDA said although the system’s overall design features help safeguard patients, Medtronic is developing updates to further mitigate these cybersecurity vulnerabilities. To date, the FDA is not aware of any reports of patient harm related to these cybersecurity vulnerabilities. The FDA also recommends that healthcare providers and patients continue to use these devices as intended and follow device labeling.
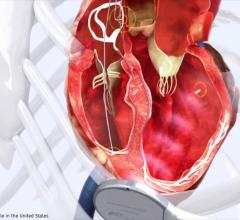
The alert concerns Medtronic’s implantable cardioverter defibrillators (ICDs) and cardiac resynchronization therapy defibrillators (CRT-Ds), devices that provide pacing for slow heart rhythms and electrical shocks or pacing to stop dangerously fast heart rhythms. The safety notice does not include any pacemakers, cardiac resynchronization pacemakers (CRT-Ps), CareLink Express monitors, or the CareLink Encore Programmer (model 29901).
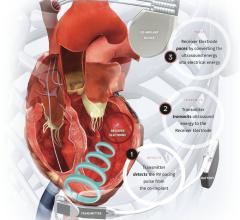
ICDs and CRT-Ds are implanted under the skin in the upper chest area with connecting insulated wires called leads that go into the heart. A patient may need an ICD or CRT-D if their heartbeat is too slow (bradycardia), too fast (tachycardia), or needs coordination to treat heart failure. The Medtronic CareLink Programmer (model 2090) is used during the implantation and regular follow-up visits for Medtronic ICDs and CRT-Ds.
The MyCareLink Monitor (models 24950 and 24952) is used to wirelessly connect to the patient's implanted cardiac device and read the data stored on the device. The transmitter, located in the patient's home, sends the patient's data to his or her physician(s) by the CareLink Network using a continuous landline, cellular, or wireless (wi-fi) Internet connection.
EP Devices Included in the Safety Alert
Affected Medtronic ICD and CRT-D device models included in the FDA safety alert are:
• Amplia MRI CRT-D, all models
• Claria MRI CRT-D, all models
• Compia MRI CRT-D, all models
• Concerto CRT-D, all models
• Concerto II CRT-D, all models
• Consulta CRT-D, all models
• Evera MRI ICD, all models
• Evera ICD, all models
• Maximo II CRT-D and ICD, all models
• Mirro MRI ICD, all models
• Nayamed ND ICD, all models
• Primo MRI ICD, all models
• Protecta CRT-D and ICD, all models
• Secura ICD, all models
• Virtuoso ICD, all models
• Virtuoso II ICD, all models
• Visia AF MRI ICD, all models
• Visia AF ICD, all models
• Viva CRT-D, all models
Affected Medtronic Programmer and Monitors models include:
• CareLink 2090 Programmer
• MyCareLink Monitor, models 24950 and 24952
• CareLink Monitor, Model 2490C
Wireless Telemetry Protocol is Main Problem
The FDA said it reviewed information concerning potential cybersecurity vulnerabilities associated with the use of the Conexus wireless telemetry protocol which is used as part of the communication method between Medtronic’s ICDs, CRT-Ds, clinic programmers and home monitors. The Conexus wireless telemetry protocol uses wireless radio frequency (RF) to enable communication between the devices
The wireless system allows Medtronic programmers and monitoring accessories to do one or more of the following:
• Remotely transmit data from a patient’s implanted cardiac device to a specified healthcare clinic (remote monitoring), including important operational and safety notifications;
• Allow clinicians to display and print device information in real-time; and
• Allow clinicians to program implanted device settings.
The FDA said the Conexus wireless telemetry protocol has cybersecurity vulnerabilities because it does not use encryption, authentication, or authorization. The FDA has confirmed that these vulnerabilities, if exploited, could allow an unauthorized individual to access and potentially manipulate an implantable device, home monitor or clinic programmer.
Medtronic is working to create and implement additional security updates to address these cybersecurity vulnerabilities beyond safety features in the current design as described in Medtronic’s security bulletin. For example, the safety features in the current design include a protocol that be activated only by the patient’s healthcare provider at a clinic. Activation times vary by patient, and an unauthorized user would need to be close to an active device, monitor or clinic programmer to take advantage of these vulnerabilities, the FDA said.
For more information see Medtronic’s Security Bulletin.
Recommendations for Healthcare Providers
The FDA said providers should continue to use the CareLink programmers for programming, testing and evaluation of ICD and CRT-D patients. There is no programmable setting that allows a clinician to turn off the Conexus wireless capabilities in the affected devices.
Providers should maintain control of CareLink programmers within your facility at all times according to your hospital information technology (IT) policies.
The FDA said providers should only use home monitors, programmers and implantable devices obtained directly from the manufacturer to ensure integrity of the system.
Providers also should remind patients to keep their home monitors plugged in. The FDA said the benefits of remote wireless monitoring of an implantable device outweigh the practical risk of an unauthorized user exploiting of these devices’ vulnerabilities. The monitor also must remain powered on to ensure timely transmission of any wireless CareAlerts programmed by the physician, and to ensure automatically-scheduled remote transmissions occur at the specified time.
Providers should operate the programmers within well-managed IT networks. The FDA recommends consulting with IT departments regarding the security of the network. For recommended actions to better secure a computer network environment, refer to www.nist.gov/cyberframework.
The FDA said reprogramming or updating the affected devices is not required at this time.
Prophylactic ICD or CRT-D replacement is not recommended and should not be performed to solely address this vulnerabilities, the FDA warned.
As with any connected medical device and especially implanted life-supporting or life-sustaining devices, discuss the risk of cybersecurity vulnerabilities with patients prior to implanting ICDs and CRT-Ds, along with other device risks and benefits, and take advantage of the latest software updates and improvements to devices.
Recommendations for Patients and Caregivers
To date, the FDA is not aware of any reports of patient harm related to these cybersecurity vulnerabilities.
The FDA recommends that patients and caregivers take the following actions:
• Use only remote monitors obtained directly from your healthcare provider or the manufacturer to ensure integrity of the system.
• Continue to keep the remote monitor plugged in at all times to ensure any wireless CareAlerts programmed by your health care provider and any automatically-scheduled remote transmissions occur in a timely manner.
• Keep track of your remote monitor.
• Get medical help right away if you feel lightheaded, dizzy, lose consciousness, or have chest pain or severe shortness of breath.
• Contact Medtronic Technical Services Monday through Friday 7 a.m. – 6 p.m. central time at (855) 275-2717 for additional information, or if you have any questions regarding the vulnerabilities.
FDA Monitoring Situation and Working With the Vendor
The FDA is working with Medtronic while they create and implement additional security updates to address these cybersecurity vulnerabilities and improve patient safety and will inform the public as new information is available.
The FDA urges manufacturers everywhere to remain vigilant about their products — companies should take steps to monitor and assess cybersecurity vulnerability risk, and be proactive about disclosing vulnerabilities and mitigations to address them. This is part of the FDA’s overall effort to collaborate with manufacturers and healthcare delivery organizations—as well as security researchers and other government agencies—to develop and implement solutions to address cybersecurity issues throughout a device’s total product lifecycle. The FDA issued recommendations to manufacturers for continued monitoring, reporting, and remediation of medical device cybersecurity vulnerabilities.
Read the full FDA safety alert.
Related Cardiac EP Device Cybersecurity Content:
Raising the Bar for Medical Device Cyber Security
The State of Healthcare Cyber Security


 July 21, 2025
July 21, 2025